Kubernetes has fundamentally changed the way DevOps teams create, manage, and operate container-based applications, but as with any production process, you can never provide enough security. This practical ebook walks you through Kubernetes security features - including when to use what - and shows you how to augment those features with container image best practices and secure network c
As businesses digitally transform, they can impose significant demands on existing mainframe applications and data requiring the need to modernize to achieve business outcomes. To meet this need for modernization which includes greater agility, efficiency, and innovation, they are choosing a hybrid cloud strategy that brings together the best of IBM Z and Cloud. IBM Z integrated into a h
For many years, SAP migrations have been a standard process. An increasing number of customers are changing their database software to IBM Db2 for UNIX, Linux, and Windows or are moving their existing Db2 based infrastructure from on-premises into the cloud. When customers move to the cloud, a heterogeneous system copy is often needed because of a change in the underlying hardware archit
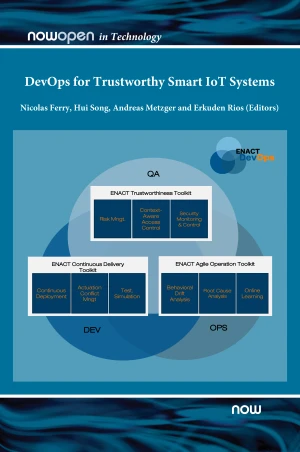
In recent years, the rising complexity of Internet of Things (IoT) systems has increased their potential vulnerabilities and introduced new cybersecurity challenges. In this context, state of the art methods and technologies for security risk assessment have prominent limitations when it comes to large scale, cyber-physical and interconnected IoT systems. Risk assessments for modern IoT
ENACT is a research project funded by the European Commission under its H2020 program. The project consortium consists of twelve industry and research member organisations spread across the whole EU. The overall goal of the ENACT project was to provide a novel set of solutions to enable DevOps in the realm of trustworthy Smart IoT Systems. Smart IoT Systems (SIS) are complex systems invo
Server virtualization is one of the most disruptive innovations of the past twenty years. It is a foundational technology in cloud computing and has been widely deployed by businesses of all sizes in both on-premises data centers and in the public cloud. Today, virtual machines (VMs) host practically any workload from mission-critical enterprise applications to dev/test environments supp
Every modern technology-driven organization understands data is one of its most valuable assets. It's no surprise, then, that the protection of that data has become an increasing concern. This concern is made much more complex, though, because organizations no longer store all their data in a single location. With the advent of modern cloud - virtualized, on-premises, hybrid, full cloud,
With the rise of the cloud, every aspect of IT has been shaken to its core. The fundamentals for building systems are changing, and although many of the principles that underpin security still ring true, their implementation has become unrecognizable. This practical book provides recipes for AWS, Azure, and GCP to help you enhance the security of your own cloud native systems. Based on h
With rapidly changing architecture and API-driven automation, cloud platforms come with unique security challenges and opportunities. In this updated second edition, you'll examine security best practices for multivendor cloud environments, whether your company plans to move legacy on-premises projects to the cloud or build a new infrastructure from the ground up. Developers, IT architec
The move to microservices is described as a seismic shift in web application development and delivery. The authors at NGINX explain that, because they believe this shift is crucial to their customers' success, they have launched a dedicated program to develop NGINX software features and development practices in support of microservices. They also recognize that there are many different a