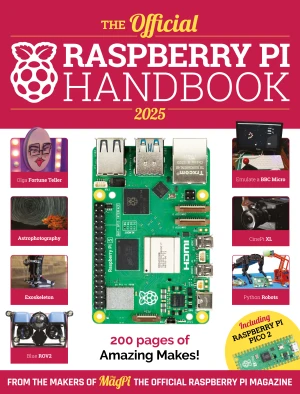
Dive into the world of Raspberry Pi with this huge book of tutorials, project showcases, guides, product reviews, and much more from the writers of The MagPi, the official Raspberry Pi magazine! Raspberry Pi Pico 2 joins Raspberry Pi 5 in this, the 2025 edition of the Official Raspberry Pi Handbook. These amazing boards can power any project you can imagine. With 200 pages packed full of
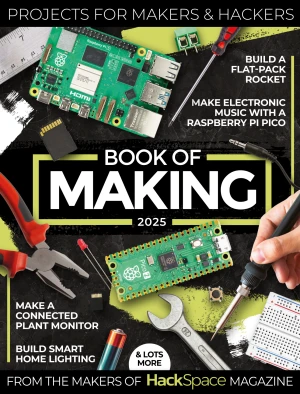
Step into the wonderful world of making with this book from the makers of HackSpace, now part of The MagPi magazine, filled with all the best projects, tutorials, and articles for makers and hackers. Book of Making 2025 distils the essence of HackSpace down to our favourite maker projects. Whether you want to build a rocket or hot air balloon, learn 3D-printed mechanical engineering, or
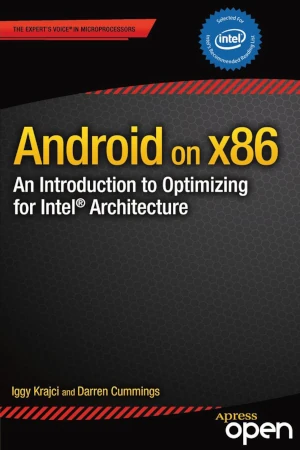
Android on x86: an Introduction to Optimizing for Intel Architecture serves two main purposes. First, it makes the case for adapting your applications onto Intel’s x86 architecture, including discussions of the business potential, the changing landscape of the Android marketplace, and the unique challenges and opportunities that arise from x86 devices. The fundamental idea is that exte
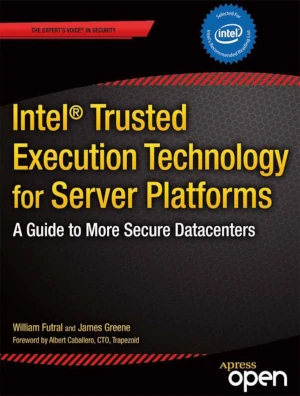
Intel Trusted Execution Technology (Intel TXT) is a new security technology that started appearing on Intel server platforms in 2010. This book explains Intel Trusted Execution Technology for Servers, its purpose, application, advantages, and limitations. This book guides the server administrator / datacenter manager in enabling the technology as well as establishing a launch control pol
Apress is proud to announce that Rethinking the Internet of Things was a 2014 Jolt Award Finalist, the highest honor for a programming book. And the amazing part is that there is no code in the book. Over the next decade, most devices connected to the Internet will not be used by people in the familiar way that personal computers, tablets and smart phones are. Billions of interconnected
Intel Xeon Phi Coprocessor Architecture and Tools: The Guide for Application Developers provides developers a comprehensive introduction and in-depth look at the Intel Xeon Phi coprocessor architecture and the corresponding parallel data structure tools and algorithms used in the various technical computing applications for which it is suitable. It also examines the source code-level opt
Mobile devices such as smartphones and tablets are set to become the main computers that virtually all people will own and carry with them at all times. And yet,mobile devices are not yet used for all computing tasks. A project at Microsoft Research was created to answer a simple question: "It is possible to create interesting apps directly on a smartphone or tablet, without using a sepa
Written for the IT professional and business owner, this book provides the business and technical insight necessary to migrate your business to the cloud using Microsoft Office 365. This is a practical look at cloud migration and the use of different technologies to support that migration. Numerous examples of cloud migration with technical migration details are included. Cloud technolog
Sensor Technologies: Healthcare, Wellness and Environmental Applications explores the key aspects of sensor technologies, covering wired, wireless, and discrete sensors for the specific application domains of healthcare, wellness and environmental sensing. It discusses the social, regulatory, and design considerations specific to these domains. The book provides an application-based appr
Managing Risk and Information Security: Protect to Enable, describes the changing risk environment and why a fresh approach to information security is needed. Because almost every aspect of an enterprise is now dependent on technology, the focus of IT security must shift from locking down assets to enabling the business while managing and surviving risk. This compact book discusses busin